By Matt Koesters
Photograpy by Andrew Higley and Illustrations by Margaret Weiner
UC’s School of Information Technology is leading the charge in Ohio to strengthen the state’s cybersecurity capabilities and talent pipeline

Advancement after advancement, technology is generation of cybertalent to meet the current and future finding new ways to creep into our lives. Nearly everyone you know carries a computer around in their pocket that’s more powerful than any desktop system from a decade ago. Our country’s money no longer changes hands in stacks of paper bills — it’s now just a bunch of ones and zeroes being moved around from one computer to the next. We now have smart homes, driverless cars and the ability to order more corn flakes with the touch of a single button.
But as our reliance on technology increases with each passing day, so too do our vulnerabilities. Computer-savvy thieves could raid our online bank accounts, hold the systems that control our energy and water supplies for ransom and, if left unchecked, bring the entire country to its knees. Unsurprisingly, the cybersecurity needs of private- and public-sector entities alike are rapidly growing. But there isn’t enough talent to meet those needs. In southwest Ohio alone, it is estimated that at least 2,000 cybersecurity jobs remain unfilled. The University of Cincinnati could soon not only bridge that gap, but become the top producer of cybersecurity talent in the Midwest.
UC is now home to the Ohio Cyber Range, an initiative of the Ohio Adjutant General’s Department and the Ohio Cyber Collaboration Committee, or OC3. The Ohio Cyber Range is a virtual environment in which everyone from kindergartners to seasoned IT professionals can learn about cybersecurity and practice defending networks against threats of all kinds.
“The increase in cyberattacks by our adversaries is getting more and more concerning,” Shawn Turskey, executive director of U.S. Cyber Command, said at the ribbon-cutting ceremony. “The Ohio Cyber Range presents an opportunity to not only leverage people, capabilities and partnerships across the cyberenterprise but also develop the next demands of this dynamic environment.”

UC officials say the Ohio Cyber Range further enhances the university’s already formidable reputation for cyber expertise. UC is one of only a handful of institutions in the country that has National Security Agency National Centers of Excellence in both cyber defense and cyber operations. Congress has relied upon the testimony of UC political science professor Richard Harknett — a prolific cybersecurity expert and former U.S. Cyber Command scholar in residence — to shape federal cybersecurity policy. Electrical engineering department head Marc Cahay heads a research group investigating cybersecurity applications for artificial intelligence and machine learning.
If you’ve never heard the phrase “cyber range” before now, don’t feel too bad. School of Information Technology Director Hazem Said had to look it up the first time he heard the phrase. During the summer of 2017, Said had received an email from John Franco, a professor of computer science and electrical engineering with the UC College of Engineering and Applied Science and the head of the NSA’s National Center of Excellence in Cyber Operations. In the email, Franco told Said that the OC3 would be visiting soon, and they were looking for a site for a cyber range.
“As I prepared for the meeting, I looked up what a cyber range is,” Said recalls. “When I read the description, it hit me immediately.” He quickly saw the connection between a cyber range and a system the school had been using for years. “I decided to show it to them in that meeting.”
FROM SANDBOX TO CYBER RANGE
Nearly a decade ago, the UC College of Education, Criminal Justice, and Human Services administration was trying to figure out how to improve the student experience for IT majors. Before the days of cloud computing and terabyte thumb drives, students were only able to work on their projects on computers on campus — and only the same computer every time, at that.
The college invested in more desktop computers and opened more labs, and they came up with a way for students to keep their work with them instead of being married to one computer, but it was less than ideal. Students carried external hard drives with all of their work on them to and from class. “There was a lot of risk involved,” recalls former CECH assistant dean Brian Verkamp, now assistant vice president of UC Information Technologies. “If the student misplaced or broke the device, they lost all of their projects.”
In 2012, two IT seniors came up with a more elegant, permanent fix. For their senior design project, Jason Gerst and Michael Latessa created a system that could be accessed remotely and provided its users with a virtual computing environment in which they had access to online storage, required software and ample processing power.
The system, which Gerst and Latessa had dubbed Sandbox, allowed users to create multiple virtual machines for the purpose of designing networks and testing network security. Sandbox used existing software and hardware, but the combination and application were both novel. Verkamp and Said, who had been contemplating an expensive cloud storage deal with Amazon, instead decided to make Sandbox a reality. “I will not say I envisioned what it would be at the time,” says Said. “We had a need in the school, so we decided to invest in this project.”
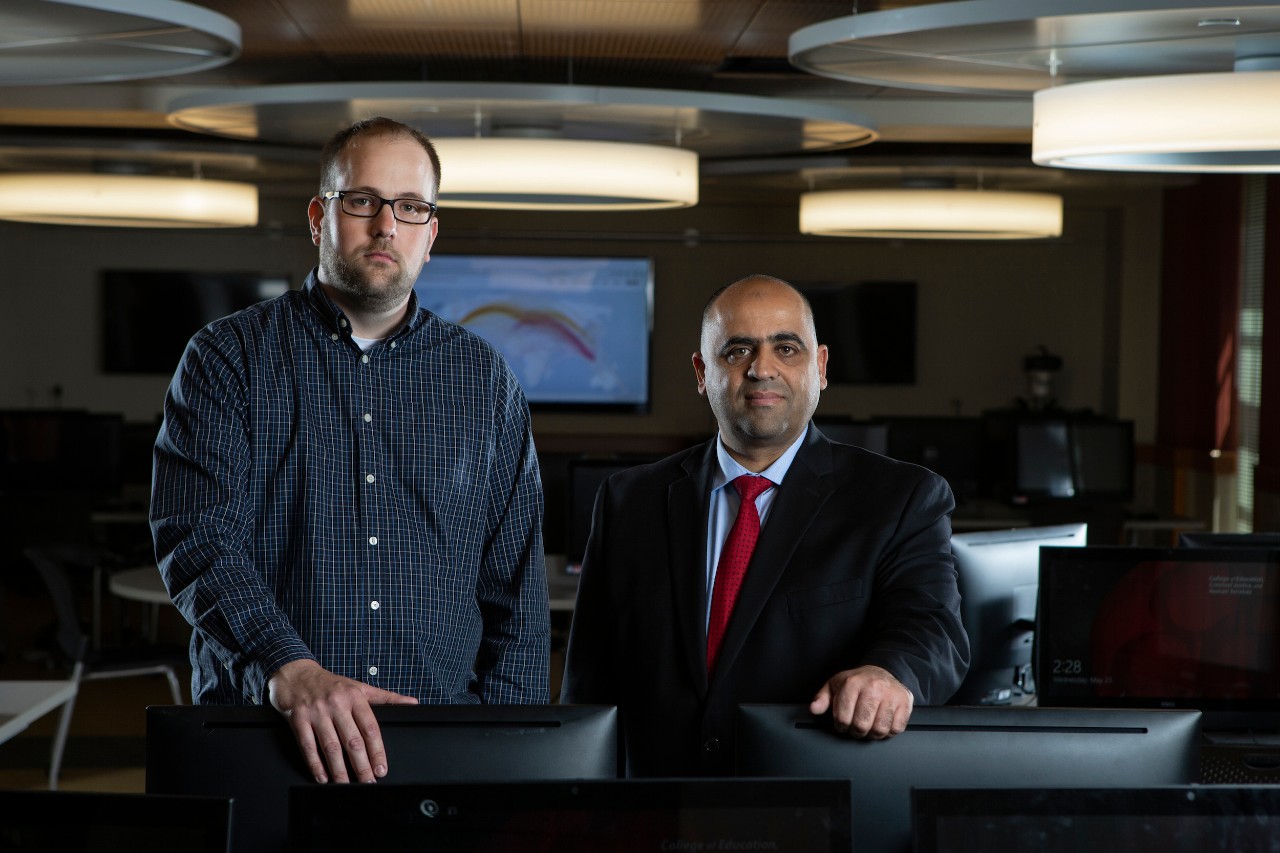
Jason Gerst, left, and Hazem Said are among those at UC leading the development of the Ohio Cyber Range on campus. Gerst now serves as the IT manager for the College of Education, Criminal Justice, and Human Services. Said is the director of UC’s School of Information Technology.
After graduating, Gerst, who had been a student worker while he pursued his degree, stayed on with the college. He now serves as CECH’s IT manager. When representatives from the OC3 came to UC for the visit, Said had Gerst come to the meeting and demonstrate Sandbox for them. “They were impressed with the system and said that it was one of the main factors in UC being awarded the grant,” Gerst says.
The Ohio Department of Higher Education awarded $1.9 million to transform Sandbox into the Ohio Cyber Range, with UC contributing another $250,000. Said says another $2 million in federal grant funding has been secured. That money will upgrade the hardware and software, as well as add features—such as the ability to simulate thousands of kinds of malicious network traffic — that are specific to cybersecurity education.
“We built a solution that over the years replaced all of our physical labs and now will serve the entire state,” adds Said.
A RANGE OF POSSIBILITIES
The Ohio Cyber Range is scheduled for official completion as a demonstration site by summer 2019, but it’s already in use. UC’s IT students and representatives from partner community colleges have access to it, as do students in the UC’s School of IT Early College Program and their instructors.
The IT Early College Program, launched fall 2017 at several Cincinnati-area high schools, gives students the chance to finish high school while also completing the first year of their IT degree at UC. Students must complete a total of nine courses with a C average or better, including six IT-related courses, to qualify and those that do receive automatic acceptance to UC as sophomores. About 200 students participated in the first year of the program, and Said estimates that about 600 will be involved in the 2018-19 school year.

Because of the Ohio Cyber Range, those students won’t need expensive computers or top-of-the-line connected devices. All they need to access the range is a web browser and an internet connection. When they are connected to the range, they have access to more computing power than any commercially available desktop or laptop computer, along with all of the software they need to do their work. “The Early College Program is not possible without this type of technology,” Verkamp says.
The School of IT’s enrollment has been on a strong upward trajectory. From fall 2015 to fall 2017, the school’s enrollment increased by 54 percent. In the 2016-17 school year, enrollment was about 600 students. It was about 800 the following year. The Ohio Cyber Range and the Early College Program promise to keep those numbers on the rise as they remove socio-economic barriers to a college degree and a well-paying job after graduation, fulfilling the state’s goal of a stronger cybersecurity talent pool.
“We’re really excited about that because for the first time, our region has a real chance of becoming a talent-surplus region,” Said says. “This is very important for economic development of our region. These are well-paid careers. These are lucrative careers. And now we’re offering that opportunity to anyone who’s willing to put the effort into it.”

Matt Koesters is a public information officer at the University of Cincinnati and contributes to UC Magazine.
Additional Credits: Thanks to photographer Andrew Higley, designer Margaret Weiner as well as web developers Kerry Overstake and Rebecca Sylvester for helping to develop and present the content contained in this piece.
FEATURES
Researcher takes innovative approach to detect lead in drinking water using carbon nanotubes.
The School of Information Technology at UC is leading the charge in Ohio to strengthen the state’s cybersecurity capabilities and talent pipeline.
Journalism student Alberto Jones shares his Boldly Bearcat story about surviving abuse to chase his dream of becoming the next Oprah.
UC’s unconventional scientist tackles remedy for cystic fibrosis and COPD with solution that could have worldwide impact.
UC prepares to celebrate its Bicentennial in 2019 — honoring the past, elevating the present and bending the future.
President Neville Pinto: Seeking the 'new and next' as UC turns 200